 ×
×


 Critical Thinking Podcast
Host
Critical Thinking Podcast
Host
 Caido
Advisor
Caido
Advisor

 Critical Thinking Podcast
Partnerships
Critical Thinking Podcast
Partnerships
Web hacking is exploiting web technologies to an attacker's advantage and/or victim's disadvantage.
Exploiting code that runs in the victim's browser. The attacker tricks the victim into executing malicious actions.
Exploiting the web server directly. The attacker sends crafted requests to abuse server-side logic.

Websites are built with HTML (HyperText Markup Language). Your browser receives raw HTML from the server and renders it into the page you see.
Tags like <h1>, <p>, and <button> tell the browser what to display. Understanding this is key to web hacking.
URLs can carry data to the server using query parameters. The ? marks where parameters begin, and each parameter is a key=value pair.
key=value
Each parameter is a key-value pair
These parameters are a key target for web hacking — they're user-controlled input sent directly to the server.
Every modern browser ships with powerful developer tools. In Chrome, open them with:
F12
Ctrl + Shift + I
Right-click → Inspect
Three tabs are essential for web hacking:
View and live-edit the page's HTML & CSS.
 to select elements directly on the page
to select elements directly on the page
Run JavaScript directly on the page.
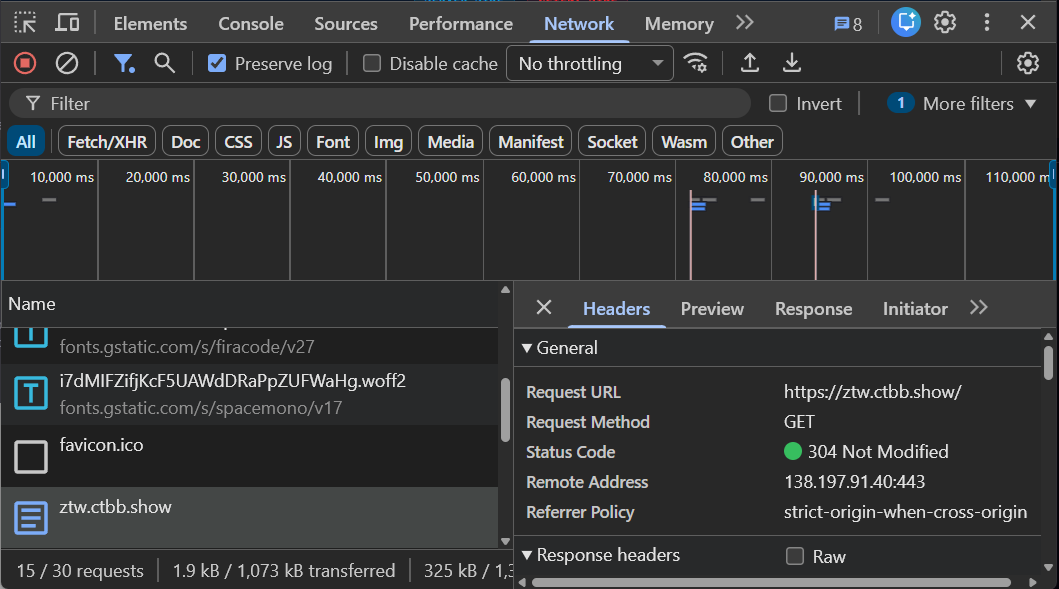
Monitor every HTTP request & response.
The victim navigates to an attacker-controlled page. The attack runs in the victim's browser.

The attacker sends an HTTP request directly to a vulnerable server.
Insecure Direct Object Reference
Access and/or modify other user's data in a website.
Broken Access Control
Circumvent poorly built access controls for a website.
Cross-Site Scripting
Inject attacker supplied HTML & JS that runs in the victim's browser.
Cross-Site Request Forgery
Force a victim's browser to perform a malicious action.
Access another user's information by manipulating object references the server exposes without proper authorization checks.
Example: You are user 1234. Change the ID in the URL to 1235 and you can see another user's private profile.
The URL contains a user ID parameter. Change the ID — the server returns any user's data without authorization.
Since IDs are sequential, an attacker can enumerate every user in the system.
for(let i=0;i<10;i++) fetch("/api/viewUser?id="+i).then(a=>a.json()).then(console.log)
Perform actions you're not supposed to be able to do by bypassing restrictions that only exist in the browser UI.
Example: You have a "Read-Only" role. The edit and delete buttons are grayed out — but the server doesn't actually check your role.
Right-click a disabled button → Inspect → delete the disabled attribute.
disabled attributeWe exploited this in the browser by removing disabled. But the real vulnerability is on the server.
The disabled attribute is just a UI hint. It prevents clicking — nothing more.
An attacker can always remove it, or skip the UI entirely and send the HTTP request directly.
The server must validate every request:
If it doesn't — that's the vulnerability.
Key takeaway: Never trust the client. The disabled attribute is a convenience, not a security control. The server must enforce authorization on every request it receives.
Open DevTools (F12) → Console → paste this one-liner to enable everything:
User input is interpreted as code. If the server doesn't sanitize input, an attacker can inject HTML & JavaScript that executes in the victim's browser.
The search endpoint reflects the q parameter directly into the HTML without sanitization.
Steal the victim's session by injecting a script that reads document.cookie.
Force the victim to take an attacker-defined state-changing action without their knowledge.
Example: You send a link to the victim. When they click it, their account gets deleted — because the browser sends the session cookie automatically.
The "Delete Account" button is just a GET request — no CSRF token, no confirmation.
Send this link to an authenticated victim. Their browser attaches the cookie automatically.
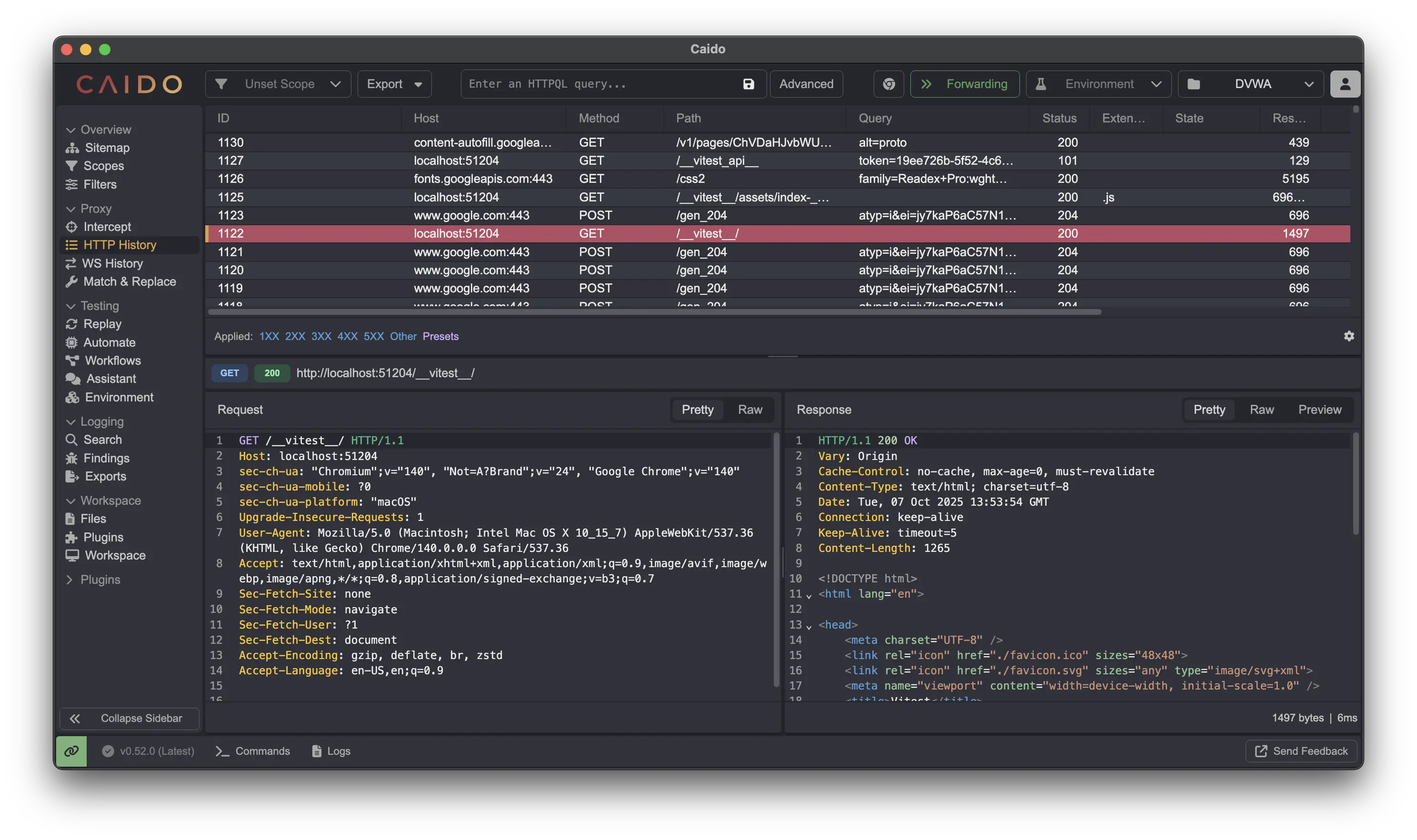
An HTTP proxy sits between your browser and the server, letting you intercept, inspect, and modify every request and response in real time.
Try additional labs at labs.cai.do to practice with an HTTP proxy.

Can you get access to the secret final lab?
Back to Lab → ×
×
